format_list_bulletedTable of Contentsexpand_more
The Invisible Runway Killers
When a startup finally secures that crucial seed or Series A venture capital, the sheer gravity of expectations physically shifts. Suddenly, the internal pressure to rapidly ship features and capture immediate market share becomes utterly immense. However, fiercely prioritizing blind speed at the absolute expense of foundational systemic structure mathematically guarantees that your startup will hit a catastrophic technological brick wall—usually right at the exact moment product-market fit is actually achieved.
At Renshok, we routinely perform deep-dive architectural rescues for startups burning massive amounts of cash just trying to keep their servers from crashing. The mistakes that cause these crises are almost never due to a lack of engineering talent; they are invariably due to a lack of elite enterprise foresight. Below, we dissect the top ten lethal mistakes we continuously audit, and exactly how to bulletproof your infrastructure against them.
Mistakes 1-3: The Architectural Catastrophes
1. Choosing 'Hype' over 'Boring' Technology: Building your core backend in an entirely unproven, v0.1 beta framework just because it heavily trended on HackerNews last week is a fatal error. Always explicitly choose incredibly battle-tested, unsexy, 'boring' technology (strictly typed TypeScript, deeply relational Postgres databases, standard Node.js). If you cannot Google a highly specific stack trace error and instantly find 50 StackOverflow answers from 2021, do not use that framework in production.
2. The Monolithic God-Database Anti-Pattern: Structuring the database with massive, deeply entangled, loosely related tables where core user authentication data, complex billing logic, and hyper-frequent application logs all violently mix together. When you inevitably need to rapidly scale your billing queries, you risk catastrophically breaking the entire application login flow. Strict bounded contexts are mandatory.
3. The 'We Will Implement Tests Later' Lie: Shipping an MVP completely devoid of automated Cypress end-to-end (E2E) tests or hardcore Jest unit tests. When your startup's codebase inevitably crosses the 50,000-line threshold, deploying any arbitrary new feature suddenly becomes terrifying because you mathematically cannot guarantee you didn’t silently break a core checkout flow. CI/CD must block untested code.
lightbulb
The Lethal Framework Lock-In
We frequently rescue late-stage startups that have become intensely, fundamentally reliant on proprietary 'No-Code' enterprise platforms. While undeniably great for initial market validation over a weekend, when you finally need genuinely custom algorithmic logic, No-Code platforms charge extortionate, compounding monthly enterprise rates and violently refuse to let you export your raw underlying code. You must build custom from day one to actually own your intellectual property (IP).
Mistakes 4-7: Development & Deployment Fallacies
4. Manual Deployments via FTP/SSH: If a senior human engineer has to actively remember the exact sequence of terminal commands to manually drag uncompiled files onto a live production server to deploy a critical update, your entire company is at extreme, systemic risk. Zero-downtime Continuous Integration/Continuous Deployment (CI/CD) pipelines explicitly configured via GitHub Actions are absolutely not a luxury; they are critically mandatory infrastructure.
5. Hardcoding Deep Production Secrets: Startups frequently, terrifyingly commit highly sensitive AWS root access keys, primary Stripe production API secrets, or master database passwords directly into public or broadly accessible Git repositories. You must use secure, heavily encrypted environment variables (e.g., dedicated Vercel Secrets or AWS Secrets Manager) exclusively, rotating them aggressively.
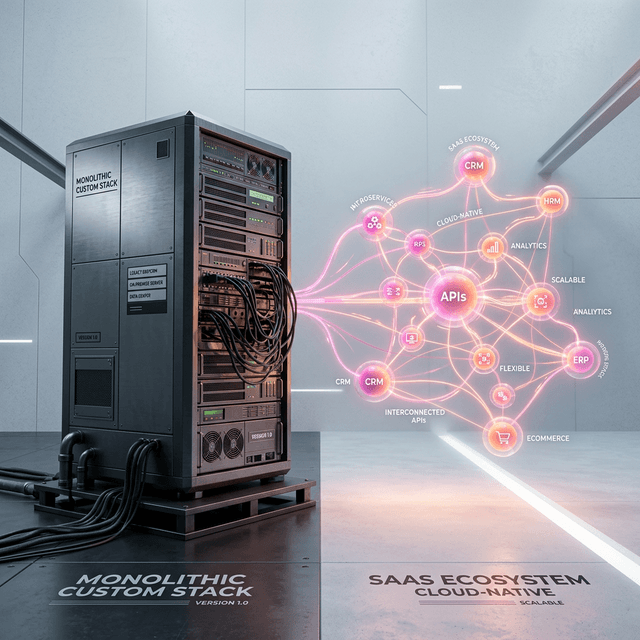
6. Premature Microservices Fracturing: Immediately splitting an untested MVP into 25 completely different, highly isolated microservices before truly understanding the macro domain logic adds absolutely massive network latency overhead and introduces sheer debugging nightmares. Start with a brilliantly structured, highly modular monolith and only mathematically cleave off microservices when explicit CPU/RAM scaling demands it.
7. Neglecting to Implement Pagination Early: Returning `SELECT * FROM users` works flawlessly when you have exactly 10 initial beta testers. It will instantly crash your aggressive Node server via an out-of-memory (OOM) exception the second you successfully reach 100,000 concurrent users. Enforce strict cursor-based server-side pagination on every single list endpoint from day zero.
| Common Startup Mistake | Renshok Elite Prevention Strategy | Architectural Risk Level |
|---|
| Manual Human Deployments | Strict Automated CI/CD Pipelines | Absolutely Critical |
| Unindexed Database Queries | Proactive SQL Query Analysis & Indexing | High - Kills CPU |
| Hardcoded Plaintext Secrets | Encrypted Cloud Secrets Manager | Critical - Company Ending |
| No-Code Vendor Lock-In | 100% Custom Stack Ownership (IP) | High - Prevents Acquisitions |
| No Automated Testing | Mandatory Cypress/Jest Coverage Gates | High - Kills Engineering Velocity |
Mistakes 8-10: Security & Scaling Oversights
8. Unindexed Deep Database Queries: The app is blazing fast with 100 users, but completely and inexplicably crashes with 10,000. Why? Because performing sequential scans over totally unindexed massive Postgres tables brutally locks the primary database CPU at 100%. You must aggressively analyze internal `EXPLAIN ANALYZE` query execution plans.
9. Blindly Trusting Client-Side Validation: Never, ever physically trust the user's browser. Validating a critical checkout form or robust user permission explicitly in the React frontend without strictly re-validating that identical payload via deep Zod schema validation concurrently on the secure Node server inevitably, mathematically leads to massive SQL injection or horrific privilege escalation vulnerabilities.
10. Avoiding Asynchronous Webhooks: Writing highly synchronous, deeply blocking server code that forcibly makes a user sit staring at a loading spinner for 30 seconds waiting for a third-party API (like generating an AI PDF or completing complex Stripe payment processing) to respond. You must fundamentally offload heavy, highly variable synchronous events to robust asynchronous message queues (SQS/Kafka) and discrete webhooks.
Ignoring these deeply structural engineering tenets is the equivalent of building a skyscraper on a foundation of quicksand. It might look incredibly polished on the surface, but the moment genuine stress is applied, the entire structure violently collapses. Elite engineering is not about typing code faster; it is about aggressively seeing three years into the future and explicitly architecting to casually survive that impending load.
Ready to Aggressively Audit Your Codebase?
Ensure your rapidly scaling startup is built on a massive foundation of concrete, not sand. Contact Renshok's senior engineers immediately for a deeply comprehensive architectural audit and a highly scalable technical mitigation strategy.