Why Growing Businesses Choose Renshok for Digital Transformation
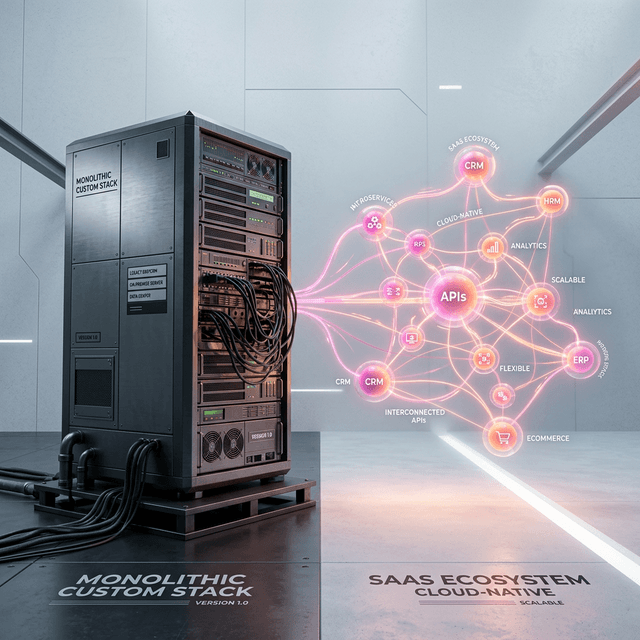
'Digital Transformation' has devolved into deeply cynical, empty marketing jargon utilized by massive consulting firms to justify simply adopting a new off-the-shelf SaaS tool or merely 'lifting and shifting' a legacy SQL database into an AWS instance. At Renshok, we view true digital transformation as something vastly more profound: the fundamental, structural restructuring of a company's core operational DNA. It is the uncompromising transition from labor-intensive, synchronous, and highly siloed human processes to heavily automated, asynchronous, and hyper-scalable digital ecosystems.
Rapidly scaling businesses inevitably slam into a critical operational juncture where blindly adding more administrative staff no longer solves their fulfillment problem—it actually creates compounding friction and dramatically reduces profit margins. Executive boards choose Renshok exclusively because they recognize they do not need another passive IT support vendor; they desperately require an elite, external engineering division capable of architecting proprietary software that serves as an unyielding, permanent competitive moat.
A massive, paralyzing fear for CTOs and stakeholders considering digital transformation is the dreaded 'big bang cutover'—turning the old legacy system off on Friday night and praying the entirely new multi-million-dollar system actually functions when the entire company logs in on Monday morning. This archaic methodology is incredibly dangerous and highly prone to catastrophic revenue loss.
Renshok inherently mitigates this immense risk by strictly utilizing modern, highly advanced deployment strategies like the 'Strangler Fig Pattern'. Instead of attempting to rewrite a massive 15-year-old local ERP overnight, we strategically extract one extremely specific, highly painful domain logic (for example, the localized inventory reserving system). We construct a hyper-modern, serverless microservice to handle exactly that one function. We then run the brand new custom architecture in absolute parallel with your legacy system, actively shadow-routing live production traffic to verify the new mathematical outputs against the old system without actually mutating any live data.
Only when the new module is certifiably, mathematically flawless do we definitively sever that specific tentacle of the legacy system. The new microservice effectively 'strangles' the old monolith piece by piece over months, guaranteeing absolute zero downtime for the enterprise and ensuring continuous, uninterrupted cash flow.
We do not build fragile 'Minimum Viable Products' (MVPs) designed merely to impress stakeholders in a wireframe presentation and subsequently collapse under the weight of actual production load. We architect enterprise-grade, highly available foundational systems from day absolute zero. Our elite engineering approach is exclusively defined by rigorous technical standards that offshore agencies simply cannot comprehend nor execute:
| Transformation Goal | Renshok Elite Implementation | Typical Offshore Agency |
|---|---|---|
| Scale Architecture | Decoupled Serverless Microservices | Rigid PHP/WordPress Monoliths |
| Data Security | Enforced Zero-Trust IAM Architecture | Basic perimeter firewall add-ons |
| Deployment Strategy | Zero-Downtime 'Strangler Fig' Transitions | Dangerous 'Big Bang' Weekend Cutovers |
| Global Latency | < 50ms via Vercel Edge Networks | 500ms+ via central shared hosting |
| Code Quality Assurance | Strict End-to-End TypeScript & Zod Validation | Typeless JavaScript prone to silent failures |
| Long Term Support | Automated CI/CD pipelines & Telemetry monitoring | Manual FTP deployments & reactive fixing |
A highly prominent reason massive enterprises consistently choose to partner with Renshok is our deep technical mastery in carefully and safely dismantling their massive legacy 'monoliths'—singular, terrifyingly massive codebases where altering a button color on the frontend inexplicably breaks the payroll calculations on the backend. This extreme systemic fragility intrinsically prevents ambitious companies from moving quickly.
By ruthlessly isolating disparate business domains—for instance, completely separating the complex billing ledger logic from the frontend user authentication logic—we grant businesses the unprecedented technical ability to safely scale, rewrite, or update highly specific parts of their sprawling architecture entirely independently. A critical failure in the email notification service will no longer ever bring down the core checkout gateway. This is the exact architectural resilience that strictly separates regional companies from unstoppable global enterprises.
Deep-dive answers into the architecture, security, and integration logic discussed in this briefing.
Partner with Renshok Software Solutions to build exceptional, scalable digital products. Whether you are scaling across India or expanding globally, our expert engineering team is ready to bring your vision to life.